Securing Your Website: A Deep Dive into Cross-Site Scripting (XSS)
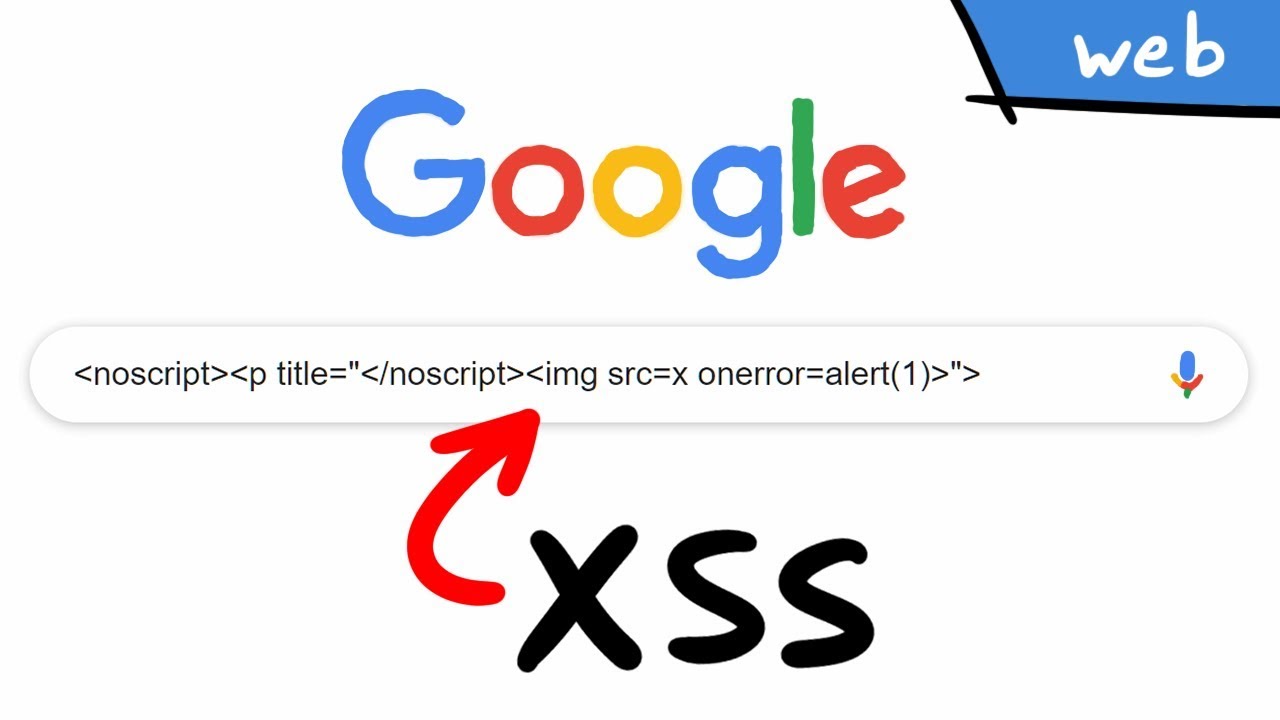
Understanding Cross-Site Scripting (XSS):
Defining XSS: Cross-Site Scripting, or XSS, stands as a critical web security vulnerability. It enables attackers to inject malicious scripts into web pages viewed by other users, leading to a spectrum of malicious activities, from data theft to unauthorized redirection.
The Mechanics Unveiled:
1. Reflected XSS:
- In a reflected XSS attack, the malicious script is embedded in a URL or a form input. When a user interacts with a manipulated link or submits a form, the script executes in their browser.
2. Stored XSS:
- Stored XSS involves permanently storing injected scripts on the target server, often in a database. When a user accesses the compromised page, the script is fetched and executed.
3. DOM-based XSS:
- DOM-based XSS exploits vulnerabilities in the Document Object Model (DOM) of a web page. The attack involves manipulating the DOM to execute scripts in the user’s browser.
Example of XSS Vulnerable code
<?php
// Vulnerable PHP code to demonstrate Cross-Site Scripting (XSS)
// Get user input from a form or another source
$user_input = $_GET['input'];
// Display the user input without proper validation or sanitization
echo "<p>User Input: " . $user_input . "</p>";
?>
Example of XSS Secure code
<?php
// Secure PHP code to prevent Cross-Site Scripting (XSS)
// Get user input from a form or another source
$user_input = $_GET['input'];
// Sanitize user input before displaying
$clean_input = htmlspecialchars($user_input, ENT_QUOTES, 'UTF-8');
// Display the sanitized input
echo "<p>User Input: " . $clean_input . "</p>";
?>
Effective Strategies Against XSS:
Securing your web applications against XSS demands a proactive and layered approach:
**1. Input Validation:
- Implement rigorous input validation to ensure user inputs are free from malicious scripts. Regular expressions and validation libraries can be effective tools.
**2. Output Encoding:
- Encode output data to neutralize potential malicious scripts. HTML entities or JavaScript encoding can prevent browsers from interpreting injected code.
**3. Content Security Policy (CSP):
- Enforce a Content Security Policy to restrict the types of content that can be executed on your website. This mitigates the impact of XSS attacks by blocking unauthorized script execution.
**4. HTTP-Only Cookies:
- Set the “HttpOnly” flag on cookies to prevent client-side scripts from accessing them, reducing the risk of session hijacking through XSS attacks.
**5. Regular Security Audits:
- Conduct routine security audits to identify and address XSS vulnerabilities promptly. Automated tools and manual testing can uncover potential weaknesses in your web application.
Conclusion:
In the dynamic realm of web security, understanding and mitigating XSS risks is paramount. By implementing best practices, staying informed about emerging threats, and maintaining a proactive security posture, you can fortify your web applications against the insidious reach of Cross-Site Scripting.
As the digital landscape evolves, fortifying your web presence against XSS is not just a security imperative; it’s a commitment to providing a safe and trustworthy online experience for your users. Stay vigilant, stay secure.

